On the 15th of January I decided to finally try myself at some game development by joining my first game jam.
The game engine that I happened to have come across was Godot, a lightweight, open-source, cross-platform game development environment.
The Godot Wild Jam is held once every 4 weeks. Every jam runs for a little over a week (starting on Friday and ends the following Sunday).
We had initially teamed up with my brother Konstantin and were sort of ready to do the game on our own. The #team-up game jam channel in Discord was full of composers and programmers but not a single artist, so we were prepared to art our way through whatever happens. Our cousin was to give us some game design ideas, text content, and playtesting.
Day Zero:
As the theme and wildcards were revealed – Nomad (with Pets, Education and Upgrades) we quickly thought “digital nomad” and, reminiscing a Russian freelance programmer game we played on Windows 95 back the days decided to make a simple click-based economics simulator, manager game. No hard animations, no art, just a ton of text, and a bit of math.
Since the jam started on Friday in the US it was actually midnight on Friday for us in Russia, so we started actual work on Saturday morning, after discussing the concept well into the night, sketching initial screens, ideas and coming up with the name: Nomadsky, like No Man’s Sky, but spoken out as a Russian surname.
The naming pun was low-hanging fruit, as out of 48 games at least two other games were named “Nomad’s Sky” 😀
Day One: GDScript.
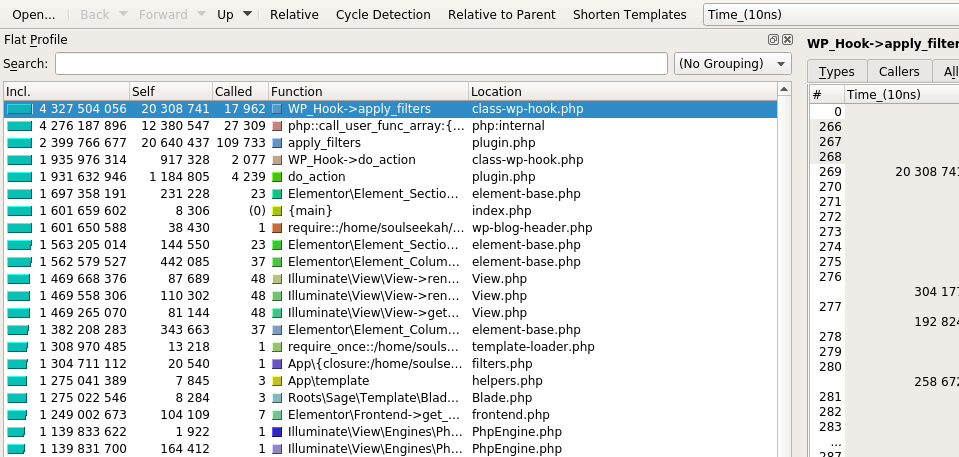
I streamed on https://www.twitch.tv/thesoulseekah diving head first into GDScript – a Python-like programming language in Godot.
The first half of day one was spent trying to use GDSCript like Python: figuring out maps, lambdas, list destructuring. None of which turned out to be a thing in Godot! Reading the source code and issues on GitHub I got carried away to the point of starting to write patches in C++ for the engine to introduce these critical features for the language. And was about to make a PR to support object key formatting in strings, when I realized I spent like 6 hours having done nothing for the actual game.
The biggest pet peeves that still remain with the language (and which I mean to send patches for) are:
- no way to add arguments when programmatically connecting signals
- print dict-based string formatting does not work with self, even though objects are accessible as dicts
Anyway. I spent the rest of the time structuring out the game code classes and a place for text content to go (job descriptions, action cards, etc.).
About 24 hours into the jam I noticed an artist looking to join a team – Merly23. I quickly explained to them what our vision for the game was and we partnered up. Merly was a bit skeptical about us finishing a game with 5 levels in it, considering nobody would work during the week on it so we had like 4-5 days maximum + whatever we could spare in the evenings and nights.
So we decided to draw level 5 and level 1 first – North Korea and New York. Those would be the starting and ending points for our hero. Nomadsky would have to freelance his way to freedom.
Day Two: Music
The second day was spent composing level music for the game. I was also streaming it and had quite some fun. I wrote music for North Korea, Mongolia, Spain. We knew that programming, text content and music-wise we’d have plenty of time, so as long as art would be pumped out quickly enough I wanted to make sure we had everything ready for all 5 levels, even though there was risk to release with as little as two levels.
I also recorded a bunch of sound effects, meowing, barking, puking, making engine noises with my mouth. I had so much fun as it was quite a while since I last touched music production (about 8 years!!).
Downtime
While we did do tiny bits of work during the evenings here and there, writing a bit content, music for New York and Spain, programming game logic and waiting for art. I also decided to play it safe and commission some local artists to draw two locations for us – Mongolia and Moscow. Merley seemed to be progressing well and we could expect 3 levels easy: New York was done by then, North Korea was being worked on and we had a weekend for Spain.
I talked to about 5 artists, none of which had pixel art or gamedev experience. Having not much choice I commissioned 4 of them to draw 2 levels. I knew that at least half of them would either be late or give up, so hedging across 4 artists was a smart choice.
Two of them did end up not delivering anything at all. One was very late on the Moscow location, so the other one did Mongolia and we had all the art about 6 hours before the deadline. All in all I spent about $100 on this external help. This was not against the rules.
Day Three: Rushing
The following Saturday we were a bit lazy and left everything for Sunday with about 12 hours to submission deadline. The first full playtests were done about 3 hours before the deadline. Final bits of art, polishing and balancing were done in quite a relaxed manner. We were in feature freeze and quite comfortable just adding graphics around, intro, credits and endgame screens, without the fear of breaking anything in the game.
We open-sourced the game on GitHub at that point and closed most of the issues we had before submitting.
By the way – Godot is a huuuge pain to work with when it comes to version control. Anything that’s done in the 2D or 3D ports, resources added to the scenes, etc. get their own resource IDs assigned, which are numeric incrementals! This means that if I add a sprite to the scene and my team mate does the same we’ll have an ID collision. So many merge tears, to the point where we had to delete and recreate resources in the scene to resolve ID conflicts.
I think Godot should use UUIDs for every node on the scenes.
I was doing a lot of text content for the game in these last 12 hours, coming up with different jobs, accidents, gifts and decisions. We submitted the game 6 minutes before the deadline and voting started for the next 4 days.
Results
I played through all the games in the jam, many were really really well done. We got really good feedback on our game as well. Only participants could vote, which ensured fair and unbiased voting. As the results were revealed we found our game placed 7th out of 48 games. Not too bad, although I had hoped at least top 5 😀
The game is available in the browser (HTML5), has Linux, Mac and Windows builds 🙂 and you can also check the source code, music and art in our GitHub repository.
Overall this was an amazing experience and we’ll definitely take part in some of the next jams easy. There was so much we didn’t really touch, like sprite animations, tiling. And 3D!
The next jam is in 19 days: https://itch.io/jam/godot-wild-jam-30, see you there, perhaps? 🙂
Published 4 years ago
by soulseekah
with one comment
tagged gamedev, gdscript, godot in Game Development
gamedev gdscript godot Game Development


 Continue reading
Continue reading