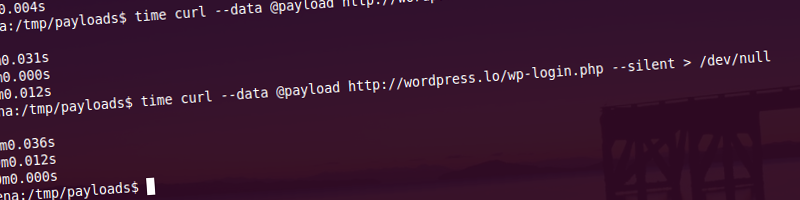
WordPress 3.3.2 maintenance release was announced yesterday. The changelog for WordPress 3.3.2 explains some of the changes and the changesets log pretty much displays all the changes done in 3.3.2.
So what the heck happened there in terms of security?
Plupload
WordPress 3.3.1 uses Plupload Version 1.5.1.1 (2011-09-27), with latest Plupload at Version 1.5.4 you can see that much could and must have gone wrong between these two. By checking out the changelog, we find the following entries:
- Fix potential vulnerability in dump.php and upload.php (too old)
- Flash: Restrict scripting ability to swf’s own domain only
- Revive temporary file removal logic in upload.php
- and possibly some others
Contents of changesets can be seen here. Not sure what we’re really looking for at this point; the WordPress changeset appears to rely on the Plupload update solely. Neal Poole promises some information it seems, which makes it even more intriguing, could the problem be not (only) in Plupload?
One of the core files in the changeset seems to be capabilities.php and it has not changed… then there’s handlers.js, with up.removeFile(file); added… no other ideas, eagerly waiting for some details.
SWFUpload
Another mystery, why are SWFUpload bugs reported to WordPress? There have been no updates to SWFUpload since September 2011 it seems. So what’s going on here? Can’t tell without decompilation of the SWF itself.
SWFobject
Changeset appears to be limited to encoding the MMredirect Flashvar, possibly related is a year-old Security Issue SDK-22303 revolving around XSS as well as this one. Latest version of SWFobject does not appear to have this change applied to it, last update was in June of 2009.
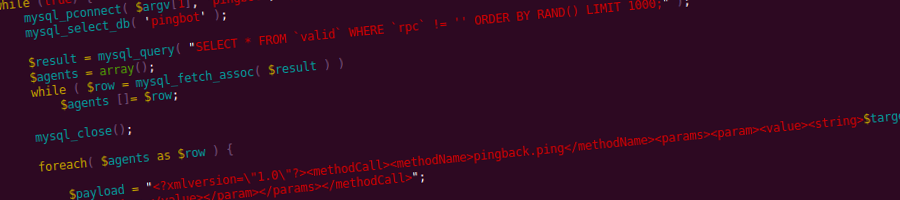
Limited privilege escalation
As the changeset shows, a non-network administrator in WordPress 3.3.1 can deactivate network-wide plugins. This is of limited use under most circumstances.
make_clickable
The make_clickable function grew in size to account for some edge case where XSS is possible in comment text.
Update: OK, so I updated to 3.3.2 and I’m still getting XSS’d from inside the comments, did I miss the point of it all or hit something else? Latest trunk with Twenty Ten/Eleven also allows script injection in comments. Whaaa…? I need to get some serious sleep, been up for over 30 hours. Enough monkey business for now.
Update: The farthest I got is injecting <a href=" www.two.com/onclick=undefined">www.five.com</a> which produces an error on the page when clicked.
Update 2: A few hours of sleep works like magic. Turns out I was logged in as administrator. That’s how I got to inject JavaScript into comments.
So that’s pretty much why the sudden update besides the couple of fixes that made it with the release. It still doesn’t feel right…
Be on the lookout for the details behind the intriguing SWF updates. Bigups go to Neal Poole, Nathan Partlan, Szymon Gruszeck, Mauro Gentile, Adam Backstrom for the patience to disclose responsibly. Much love to the core and the security teams that make it of utmost importance to keep WordPress users safe. Thank you.
Published 13 years ago
by soulseekah
with 5 comments
tagged core, security in WordPress
core security WordPress